 PCI DSS Level One #1 Certificate
PCI DSS Level One #1 Certificate
Requirement and Process
What is PCI DSS?
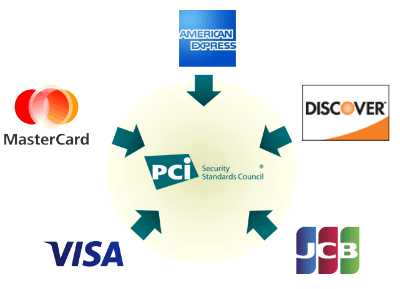
PCI DSS (Payment Card Industry Data Security Standard) is a set of rules that ensure online credit card transactions are protected & safe from hackers. These rules apply to every business that processes, stores, or transmits credit card information over the internet. It was developed in 2004 by a group of payment card issuers (American Express, Visa, Discover, JCB, and MasterCard) to reduce risks related to Payment card fraud and hacking.
- PCI DSS Compliance means you implemented the best practices in your work environment to keep your systems off the security breaches.
- PCI DSS Certificate means that your systems are secured & protected. Your customers can trust you to enter their credit cards on your platform.
- PCI Compliance Seal improves your reputation which leads to buyers’ trust.
PCI DSS Compliance for Level 1 Merchants:
It is the highest and most stringent level of PCI DSS. To be eligible to level one PCI DSS, you may consider the following criteria:
PCI DSS Level #1 Criteria:
- The number of card transactions is (VISA Transactions >6 million, or > 2.5 million American Express, or >1 million JCB) per year.
- OR you store/process cardholder's sensitive data in your systems.
- OR your firm experienced a cyber attack that led to access to the cardholder's sensitive data.
PCI DSS Level #1 Requirements:
The PCI DSS requirements aim to enhance the security of payment card account data. It represents the key steps to following the security best practices.
|
Goal |
PCI DSS Requirements |
|
Build and Maintain Secure Networks and Systems |
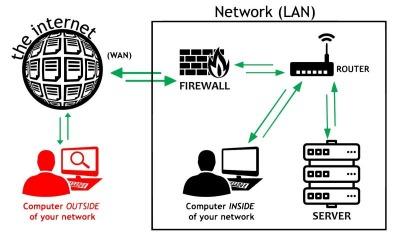
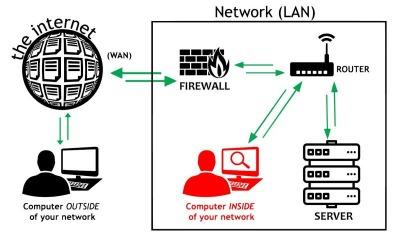
1. Install and maintain a firewall configuration to protect cardholder’s data. 2. Do not use vendor-supplied defaults for system passwords and other security parameters. |
|
Protect Cardholder’s Data |
3. Protect stored cardholder’s data. 4. Encrypt transmission of cardholder’s data across open, public networks. |
|
Maintain a Vulnerability Management Program |
5. Protect all systems against malware and regularly update anti-virus software or programs. 6. Develop and maintain secure systems and applications. |
|
Implement Strong Access Control Measures |
7. Restrict access to cardholder’s data by business needs. 8. Identify and authenticate access to the system’s components. 9. Restrict physical access to cardholder’s data.. |
|
Regularly Monitor and Test Networks |
10. Track and monitor all access to network resources and cardholder’s data. 11. Regularly test systems and processes of security. |
|
Maintain an Information Security Policy |
12. Maintain a policy that addresses information security for all personnel. |
PCI DSS Process?
First, you need to choose one of the PCI-Approved Qualified Security Assessor (QSA) companies to conduct the audit and provide the RoC by the end of the process which is considered the PCI DSS compliance proof certificate.
Next, you will need to conduct the following types of scans as per the QSA requests:
Scan Types required for PCI DSS Level #1 merchants
One benefit of regularly doing this scan is that you take a proactive approach to protect your network from known vulnerabilities.
The internal examination also provides insights into the patch management process making sure there are no third-party patches or known vulnerabilities such as DROWN, EternalBlue, or Heartbleed.
How Daam Al-Arabia can help you?
Our security experts at Daam Al-Arabia can help you select the right QSA, ASV, and penetration test firms for your business and get your PCI DSS certificate in Saudi Arabia as quickly as possible.
We also offer robust, cost-effective, PCI DSS approved solutions:
- Conducting security assessments.
- Vulnerabilities, external, and internal scans.
- Penetration tests.
Our wide range of services will not only help you prepare for PCI DSS compliance but will improve the overall security of your organization.




Daam Al-Arabia
Our Experts Always Here to Help You.